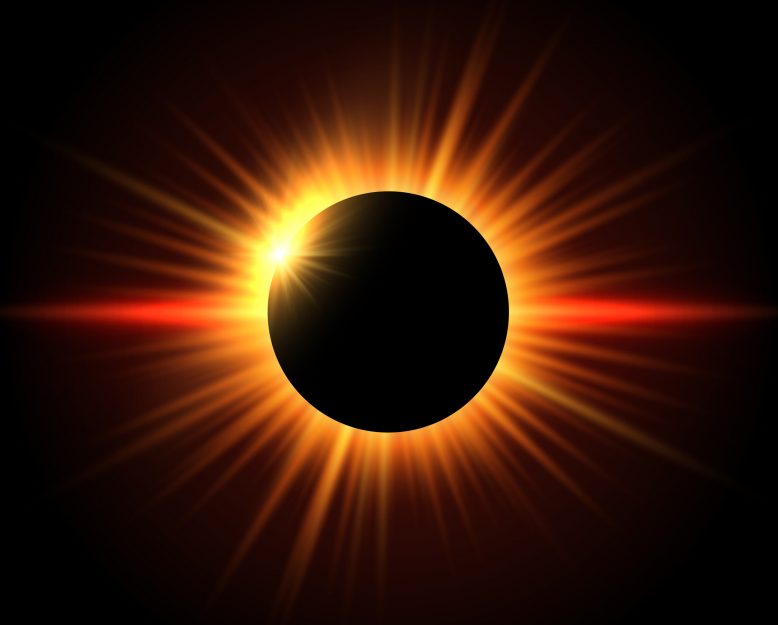
On April 8, 2024, a total solar eclipse will cross North America, hitting the Midwest region at approximately 2:00 p.m. EDT. As we have done in the past, Zimcom will be celebrating this awe-inspiring celestial event.
Just as the moon eclipses the sun, private cloud and public cloud security can be obscured by blind spots, leaving organizations vulnerable to unseen threats. These blind spots, much like the darkness of an eclipse, pose significant concerns for businesses navigating the complex terrain of secured cloud hosting environments.
4 Major Cloud Security Blind Spots
Much like the darkness of a solar eclipse obscures the sun’s brilliance, these cloud security blind spots conceal critical information that could mitigate security threats. Gaining insight into these cloud security blind spots is essential for implementing robust security measures that safeguard against unseen threats and ensure the integrity, confidentiality, and availability of critical assets in the cloud.
Blind Spot #1: Identity and Access Management
Identity and access management (IAM) strategies, encompassing user and machine identities, are foundational to cloud security. From robust password management to multifactor authentication (MFA), IAM frameworks ensure that only authorized individuals and systems can access sensitive data and applications.
Blind Spot #2: Control Over Cloud Data
Effective control over cloud data involves comprehensive measures, such as data classification, loss prevention protocols, and encryption. Network and device security, including encryption and virtual private networks (VPNs), form crucial barriers to protect data integrity and confidentiality.
Blind Spot #3: Access to Cloud Data and Applications
Implementing stringent access control mechanisms, anomaly detection systems, malware prevention measures, and privileged access controls are essential for safeguarding against unauthorized access and data breaches.
Blind Spot #4: Visibility Into Cloud Data
When it comes to cloud security, visibility is paramount. Organizations must employ robust monitoring and alert systems, such as security incident and event management (SIEM) platforms and security operations centers (SOCs), to detect and respond to suspicious activity promptly. Additionally, disaster recovery and business continuity planning are essential safeguards against potential data loss or downtime.
Ready to protect your data?
Mitigating the Risk of Unmanaged Cloud Security
Unmanaged cloud security blind spots present significant risks to organizations, potentially leading to data breaches, compliance violations, and reputational damage.
Taking a Proactive Approach to Cloud Security
Zimcom adopts a holistic security approach that prioritizes the seamless integration of visibility, control, access, and compliance to ensure robust protection in cloud environments. Through enhanced visibility, Zimcom empowers clients with real-time insights into their cloud infrastructure, enabling them to monitor and analyze data flows, user activities, and system behaviors effectively.
Learn more about what proactive cloud security entails.
Upholding Industry Best Practices
Zimcom emphasizes stringent control mechanisms, enforcing granular access controls and encryption protocols to safeguard sensitive data from unauthorized access or manipulation. By combining these elements, Zimcom creates a fortified security framework that mitigates risks and fortifies defenses against evolving cyberthreats.
Furthermore, Zimcom implements best practices for cloud security to ensure the efficacy of its protective measures. Leveraging industry-leading technologies and methodologies – like those provided by the Cloud Security Alliance – Zimcom devises tailored security solutions that address the unique challenges and requirements of each client. From ensuring SOC2 compliance to conducting regular security assessments and audits, Zimcom employs a proactive stance towards risk management.
Zimcom recognizes the critical role of aligning technological solutions with organizational policies and standards to maintain regulatory compliance and uphold industry best practices. By harmonizing technology and policy, Zimcom ensures that security measures are seamlessly integrated into existing workflows and operations, fostering a culture of security awareness and accountability across the organization.
Trust and Transparency
Zimcom’s commitment to trust and transparency is encapsulated in its TRUST acronym:
T: Technology that empowers your business
R: Reliable support when needed
U: Understanding your needs for a tailored solution
S: Security measures to protect your data
T: True partnership built on respect and personal attention
Expert management, like that provided by Zimcom, is indispensable in navigating the complexities of cloud security. By leveraging cutting-edge technology, providing reliable support, understanding individual client needs, implementing robust security measures, and fostering true partnerships, Zimcom ensures that clients navigate the cloud with confidence.
7 essentials to protect your business.
Illuminating the Path Forward
As the solar eclipse passes and daylight returns, the significance of trust and transparency in cloud security remains undiminished. Zimcom’s unwavering commitment to transparency and security ensures that organizations navigate the cloud with confidence, free from the shadows of uncertainty. Just as the sun emerges from behind the moon, so too can organizations emerge from the darkness of cloud security blind spots, guided by the expertise and trustworthiness of a reliable partner.


